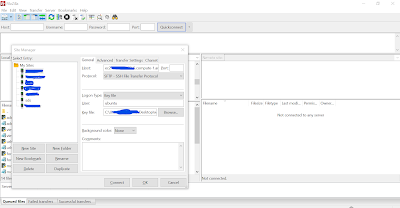
You can connect with aws ec2 server via filezila using below process.. Step 1:- Collect server informations. First you have to collect some required informations for your AWS instance like public DNS, PEM file, User etc… If you use ubuntu image for creating a instance then you can use ubuntu as defaul user. PEM file:- This is the file use for creating a instance. you have to save in to your computer for future use. Public DNS:- You can either use public elastic IP address or its public DNS. Read More: How…
Month: April 2021
The Platform Mindset in API Product Management
The COVID-19 pandemic accelerated the need for organizations to adopt a digital-first strategy, with digital transformation becoming a top priority overnight. According to the McKinsey Global Survey 2020, companies rapidly digitized internal operations and expanded digital product portfolios. APIs (Application Programming Interfaces) serve as the backbone of this transformation, acting as intermediaries that enable seamless data exchange between software systems, fostering connectivity and unlocking new business opportunities. Connecting the Dots The Best of Breed (BoB) approach emphasizes integrations as a core component of product strategies. Tools like HubSpot’s CRM integrate…
How To Host A Website On AWS using Elastic Load Balancers (ELB)?
I found most developers struggling to host a website on AWS. Even some of my friends ask me several time to make them understand some easiest way to host a website on AWS. Also many of developers are fears to host their websites on AWS due to high charges associated on AWS. But you have all the control on AWS. So you can minimise the charges as you wants.I have already describe a simplest process for hosting a website on AWS using vista panel. you can check Easy Process to Host…
Get Stand-out Service from Programming Assignment Help to Nurture your Career
In an era when science and technology are at their peak, it is a must you have knowledge about these things else you will lag behind the others. Where Artificial Intelligence has taken up almost all the work of human beings, it makes it difficult to survive in the world today without the knowledge of computers. Coding and programming are introduced into the curriculum of school-going students from standard fourth or fifth. This itself proves how important it is along with normal studies. In the early stages, we are taught…
Are Portable Monitors Good for Coding?
The short answer is yes, they are good for coding as it is difficult for a programmer to code on a single screen. A portable monitor acts as a second display making coding easier. If you are a programmer, you probably know how stressful it is to work on a single screen. A portable monitor often at times is the perfect solution for most programmers as it is portable, travel-friendly, and convenient to work with. Also, the added benefit that they often don’t require any extra power source is…
How Social Media Monitoring Captures Marketing Ideas: Explained by NetbaseQuid
When it comes to the internet, information seems to flow freely around. Social media marketing (SMM) is a method that allows businesses to track what is going viral. Following what is being said is a must in today’s instant reaction world. There are tools available, and at first, it may not be obvious what the benefits are of utilizing these applications. Inside Knowledge When an operation delves into social media monitoring, internal information gets revealed. Seeing what is being shared across social platforms is valuable on many levels. It gives…
Top 10 Most Powerful Website VAPT Tools In 2021
Vulnerability Assessment and Penetration Testing (VAPT) is a very important security practice. A website security audit / VAPT helps one identify all the vulnerabilities and potential risks of intrusion on a website. Using this information, you can improve your security system and wire it to block all kinds of cyberattacks. Statistics show that about 70% of websites/applications have vulnerabilities that are either exploited or can potentially be exploited. Therefore, identifying vulnerabilities and patching them must be your top priority if you don’t wish to lose important data and customers. However,…
Why Do You Need a Joomla Firewall?
Like all other CMS platforms, Joomla has had its share of cyber issues that require the frequent upgradation of security facilities and constant monitoring by security experts. The impact can be disastrous for those using the platform without implementing reliable security measures as vulnerabilities in the platform cause both short-term and long-term issues that cannot be resolved quickly. The best strategy you can undertake as a Joomla platform user is to make sure all available and proven security measures are implemented and followed up on regularly. You can further automate…